Table of Contents
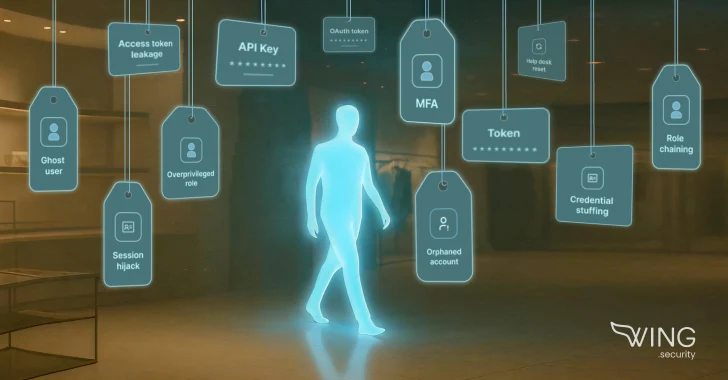
From overprivileged admin roles to long-forgotten vendor tokens, these attackers are slipping through the cracks of trust and access. Here’s how five retail breaches unfolded, and what they reveal about…
In recent months, major retailers like Adidas, The North Face, Dior, Victoria’s Secret, Cartier, Marks & Spencer, and Co‑op have all been breached. These attacks weren’t sophisticated malware or zero-day exploits. They were identity-driven, exploiting overprivileged access and unmonitored service accounts, and used the human layer through tactics like social engineering.
Attackers didn’t need to break in. They logged in. They moved through SaaS apps unnoticed, often using real credentials and legitimate sessions.
And while most retailers didn’t share all the technical details, the patterns are clear and recurring.
Here’s a breakdown of the five recent high-profile breaches in retail:
1. Adidas: Exploiting third-party trust
Adidas confirmed a data breach caused by an attack on a third-party customer service provider. The company said customer data was exposed, including names, email addresses, and order details. No malware. No breach on their side. Just the blast radius of a vendor they trusted.
How these attacks unfold in SaaS identities:
SaaS tokens and service accounts granted to vendors often don’t require MFA, don’t expire, and fly under the radar. Once access is no longer needed but never revoked, they become silent entry points, perfect for supply chain compromises that map to tactics like T1195.002, giving attackers a way in without setting off alarms.
Security takeaway:
You’re not just securing your users. You’re securing the access that vendors leave behind, too. SaaS integrations stick around longer than the actual contracts, and attackers know exactly where to look.
2. The North Face: From password reuse to privilege abuse
The North Face confirmed a credential stuffing attack (MITRE T1110.004) where threat actors used leaked credentials (usernames and passwords) to access customer accounts. No malware, no phishing, just weak identity hygiene and no MFA. Once inside, they exfiltrated personal data, exposing a major gap in basic identity controls.
How these attacks unfold in SaaS identities:
SaaS logins without MFA are still everywhere. Once attackers get valid credentials, they can access accounts directly and quietly, no need triggering endpoint protections or raising alerts.
Security takeaway:
Credential stuffing is nothing new. It was the fourth credential-based breach for The North Face since 2020. Each one is a reminder that password reuse without MFA is a wide-open door. And while plenty of orgs enforce MFA for employees, service accounts, and privileged roles, many times they go unprotected. Attackers know it, and they go where the gaps are.
Want to go deeper? Download the ‘SaaS Identity Security Guide‘ to learn how to proactively secure every identity, human or non-human, across your SaaS stack.
3. M&S & Co-op: Breached by borrowed trust
UK retailers Marks & Spencer and Co-op were reportedly targeted by the threat group Scattered Spider, known for identity-based attacks. According to reports, they used SIM swapping and social engineering to impersonate employees and trick IT help desks into resetting passwords and MFA, effectively bypassing MFA, all without malware or phishing.
How these attacks unfold in SaaS identities:
Once attackers bypass MFA, they target overprivileged SaaS roles or dormant service accounts to move laterally within the organization’s systems, harvesting sensitive data or disrupting operations along the way. Their actions blend in with legitimate user behavior (T1078), and with password resets driven by help desk impersonation (T1556.003), they quietly gain persistence and control without raising any alarms.
Security takeaway:
There’s a reason identity-first attacks are spreading. They exploit what’s already trusted, and often leave no malware footprint. To reduce risk, track SaaS identity behavior, including both human and non-human activity, and limit help desk privileges through isolation and escalation policies. Targeted training for support staff can also block social engineering before it happens.
4. Victoria’s Secret: When SaaS admins go unchecked
Victoria’s Secret delayed its earnings release after a cyber incident disrupted both e-commerce and in-store systems. While few details were disclosed, the impact aligns with scenarios involving internal disruption through SaaS systems that manage retail operations, like inventory, order processing, or analytics tools.
How these attacks unfold in SaaS identities:
The real risk isn’t just compromised credentials. It’s the unchecked power of overprivileged SaaS roles. When a misconfigured admin or stale token gets hijacked (T1078.004), attackers don’t need malware. They can disrupt core operations, from inventory management to order processing, all within the SaaS layer. No endpoints. Just destruction (T1485) at scale.
Security takeaway:
SaaS roles are powerful and often forgotten. A single overprivileged identity with access to critical business applications can trigger chaos, making it crucial to apply stringent access controls and continuous monitoring to these high-impact identities before it’s too late.
5. Cartier & Dior: The hidden cost of customer support
Cartier and Dior disclosed that attackers accessed customer information via third-party platforms used for CRM or customer service functions. These weren’t infrastructure hacks; they were breaches through platforms meant to help customers, not expose them.
How these attacks unfold in SaaS identities:
Customer support platforms are often SaaS-based, with persistent tokens and API keys quietly connecting them to internal systems. These non-human identities (T1550.003) rarely rotate, often escape centralized IAM, and become easy wins for attackers targeting customer data at scale.
Security takeaway:
If your SaaS platforms touch customer data, they’re part of your attack surface. And if you’re not tracking how machine identities access them, you’re not protecting the frontlines.
Final Thought: Your SaaS identities aren’t invisible. They’re just unmonitored.
Your SaaS identities aren’t invisible; they’re just unmonitored. These breaches didn’t need fancy exploits. They just needed a misplaced trust, a reused credential, an unchecked integration, or an account no one reviewed.
While security teams have locked down endpoints and hardened SaaS logins, the real gaps lie in those hidden SaaS roles, dormant tokens, and overlooked help desk overrides. If these are still flying under the radar, the breach already has a head start.
Wing Security was built for this.
Wing’s multi-layered platform continuously protects your SaaS stack, discovering blind spots, hardening configurations, and detecting SaaS identity threats before they escalate.
It’s one source of truth that connects the dots across apps, identities, and risks, so you can cut through the noise and stop breaches before they start.
👉 Get a demo of Wing Security to see what’s hiding in your SaaS identity layer.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Twitter and LinkedIn to read more exclusive content we post.